Linux Kernel Vulnerability Exploiting - Kernelpop
What is Kernelpop ?
kernel privilege escalation enumeration and exploitation framework
Supports the following OS’s
- Linux
- Mac
- Windows - Coming soon
Example of enumeration to root
default mode (passive)
The default mode runs with the command python3 kernelpop.py. This processes information about the host kernel and compares it to the known kernel exploits available to the program. It then outputs a list of potentially useful vulnerabilities and attached exploits.
exploit mode NEW (active)
The exploit mode is run with the -e flag. This dynamically compiles and runs the exploit source code with stdio interactions inside the program! It can catch interrupts from short-stopped attempts as well
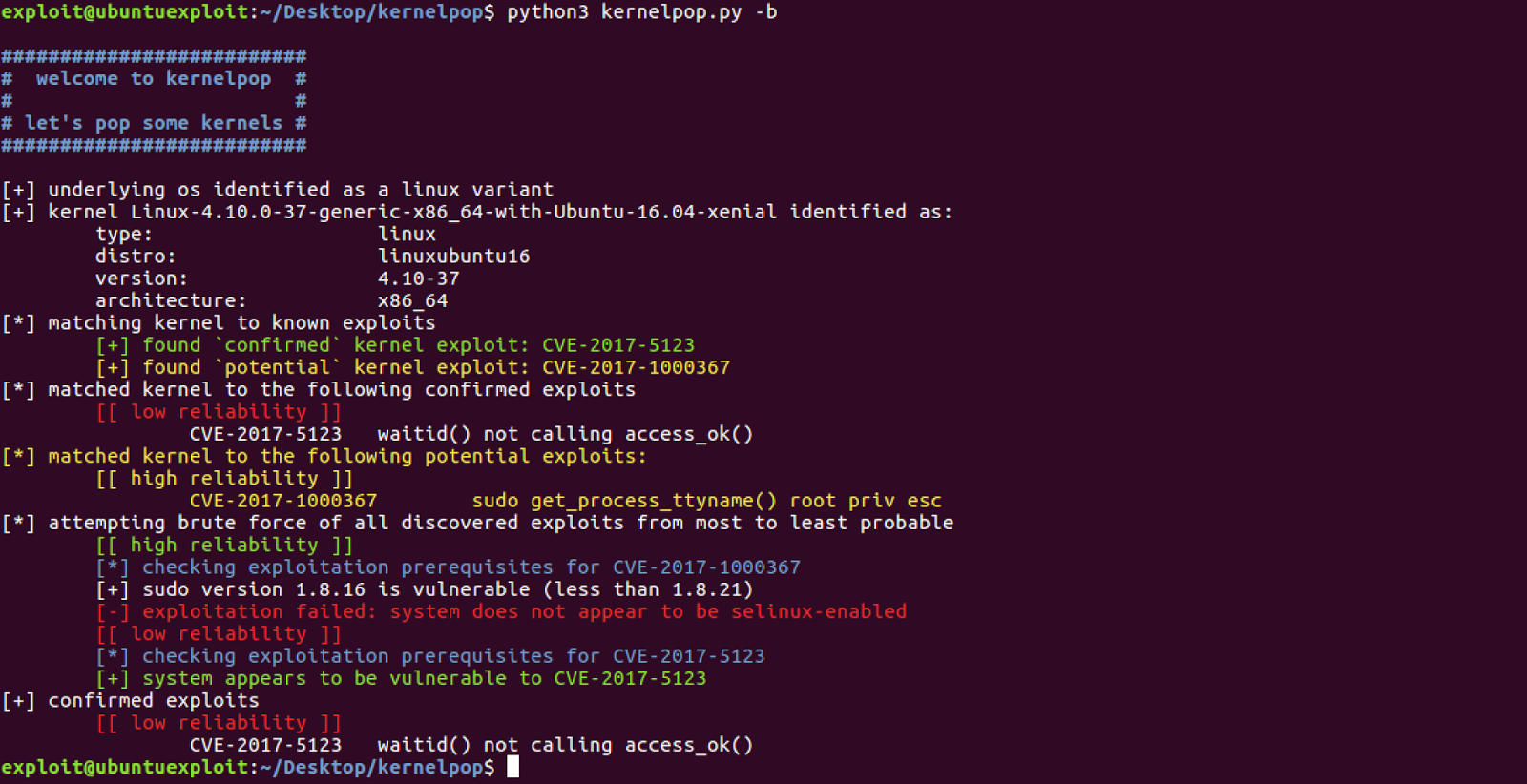
brute-enumeration mode (active)
The brute-enumeration mode performs the same checks as the default mode, but then goes beyond and checks the computer for exploit prerequisites to see if the operating system is set up in the required vulnerable state for successful exploitation.
brute-enumeration mode (active)
The brute-enumeration mode performs the same checks as the default mode, but then goes beyond and checks the computer for exploit prerequisites to see if the operating system is set up in the required vulnerable state for successful exploitation.
input mode (passive)
The input mode allows you to perform enumeration with just the output of a uname -a command, which makes it useful as a host-side only enumeration tool.
mac enumeration example
currently supported CVE’s:
- CVE2017-1000379
- CVE-2017-1000373
- CVE-2017-1000372
- CVE-2017-1000371
- CVE-2017-1000370
- CVE-2017-1000367
- CVE-2017-1000112
- CVE-2017-7308
- CVE-2017-6074
- CVE-2017-5123
- CVE-2016-5195
- CVE-2016-2384
- CVE-2016-0728
- CVE-2015-1328
- CVE-2014-4699
- CVE-2014-4014
- CVE-2014-3153
- CVE-2014-0196
- CVE-2014-0038
- CVE-2013-2094
- CVE-2010-4347
- CVE-2010-2959
- CVE-2009-1185
exploit sources
https://github.com/SecWiki/linux-kernel-exploits
Recent Posts
Tags
Categories
Active directory Burpsuite Cheatsheet Crackmapexec Empire Events Exploit File transfer Iis Implants Kcsec Kerberos Kernelpop Ksec Ksec snapshot Lab Metasploit Metasploitable Msfvenom Netcat Nfc & rfid Nikto Nmap Pivoting Privilege escalation Proxmark Proxychains Redteam Responder Rubber ducky Shells Sqlmap Sshutle Thefatrat Toolkit Webapp Windows domain Xss