Proxmark 3 RDV2 Setup OSX
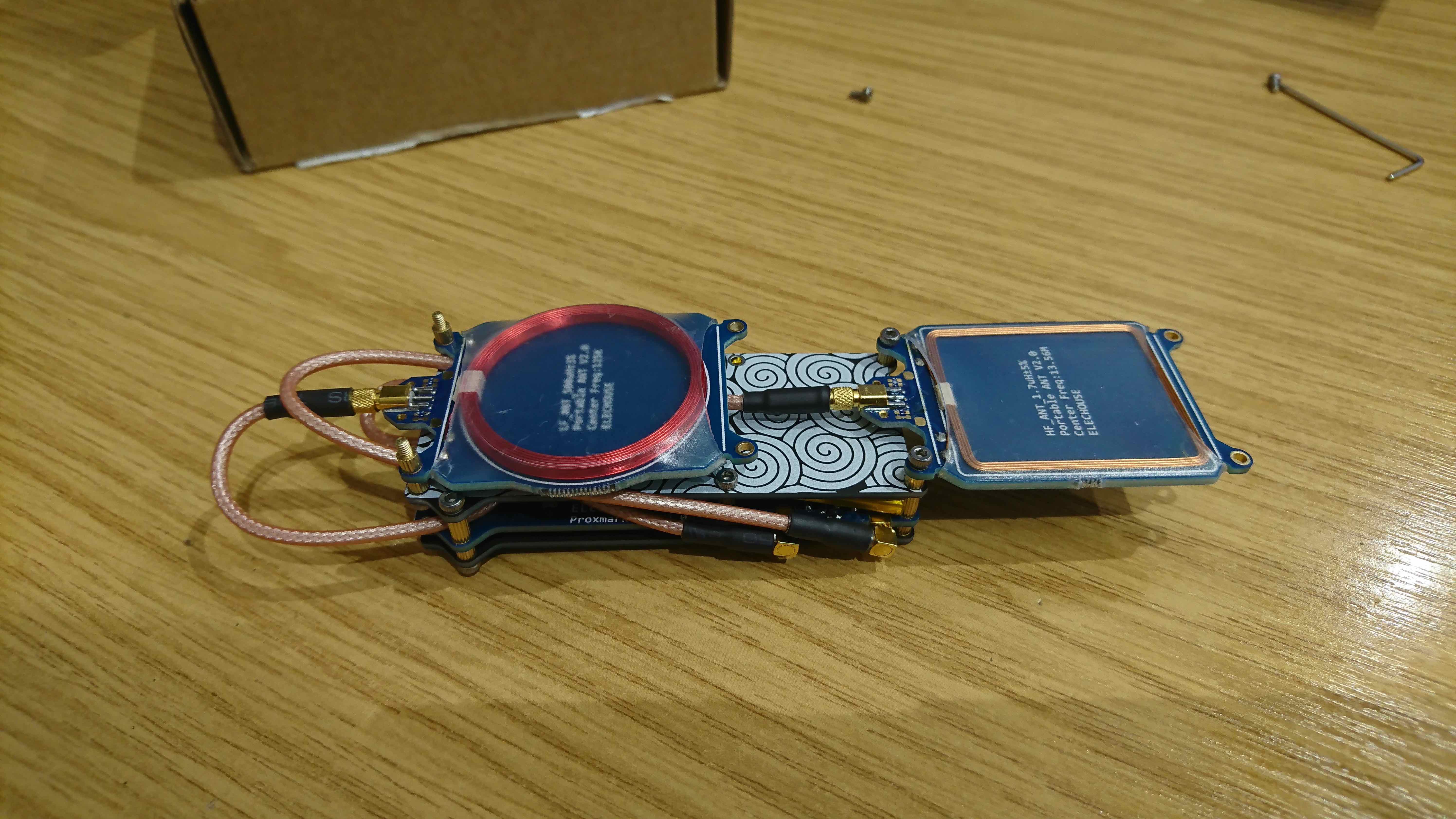
Proxmark 3 Dev unboxing
So after a few weeks my ELECHOUSE proxmark 3 dev arrived.

Shortly after assembling it, the supplied battery (Part of the extra pack) was actually bigger than in the assembly guide. After a bit of tinkering, managed to get it to fit.



How it looks all tucked in.
I opted for this setup to mess around with seemed a good way of keeping it all contained with an easy way to read LF/HF tags while connected.
Setup on OSX - Brew
So setting up the Proxmark was easy enough to do with the use of brew.
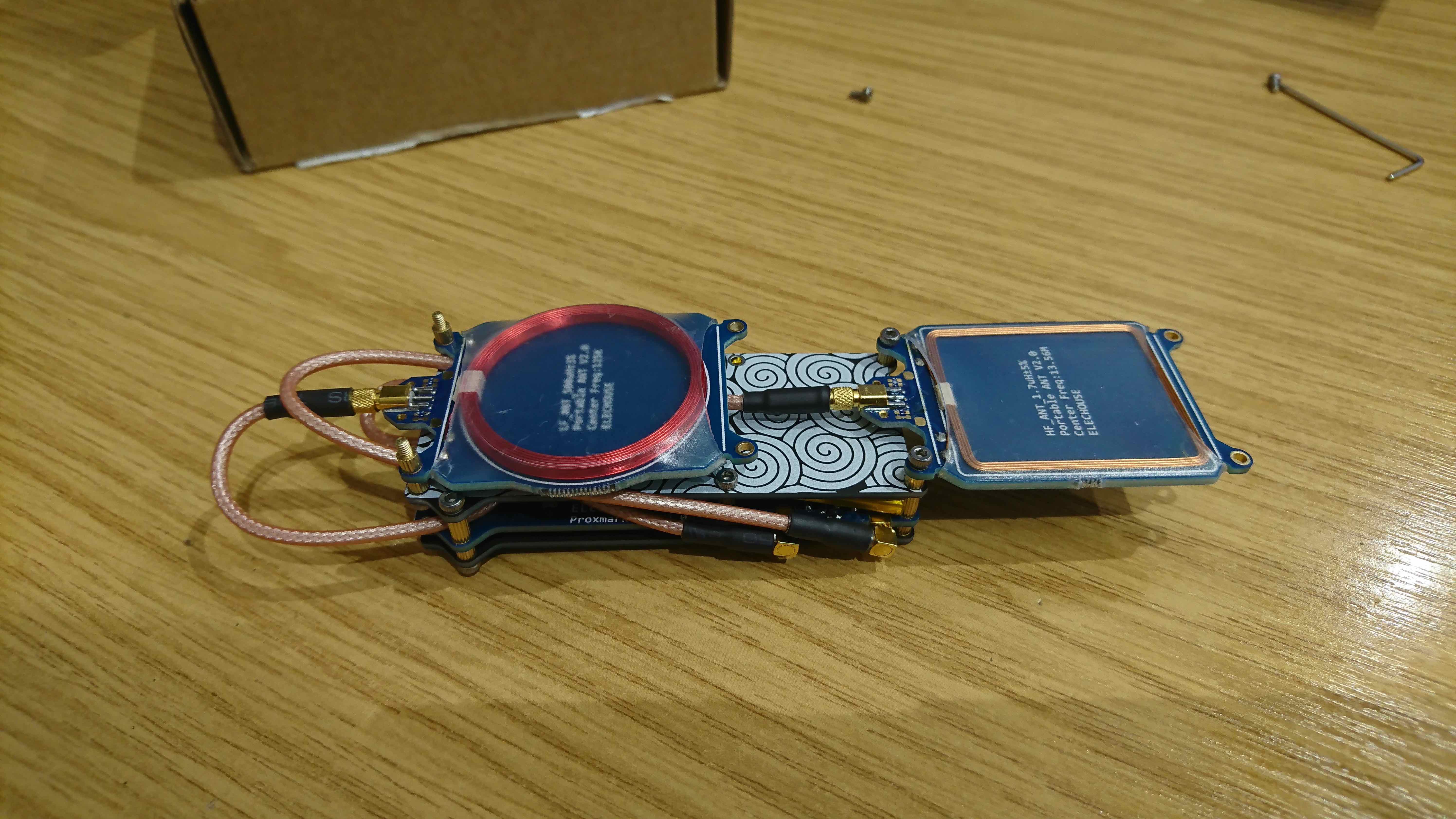
Once plugged in you can find it listed as a “communication device” as shown bellow,
system_profiler SPUSBDataType
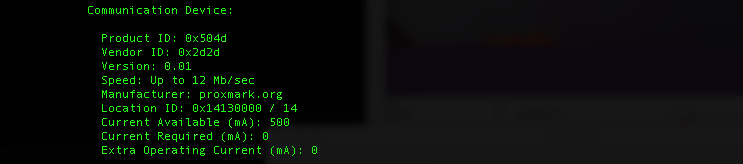
Install homebrew if you haven’t yet already done so: http://brew.sh/
Tap proxmark repo:
brew tap proxmark/proxmark3
Install Proxmark3:
for stable release
brew install proxmark3
for latest non-stable from GitHub (use this if previous command fails)
brew install --HEAD proxmark3
Updating Proxmark
The firmware will be downloaded and built as part of the brew proxmark install. All the files are kept under the following directory
/usr/local/Cellar/proxmark3/X.X.X
This will depend on the version that is downloaded at the time.
Mine is “3.0.1”
cd to the Proxmark3 directory
cd /usr/local/Cellar/Proxmark3/3.0.1/
Press the button on the Proxmark3 and KEEP IT PRESSED while you reconnect it to USB. After five seconds you can release the button. Then, figure out the device name of the Proxmark3:
ls /dev/cu*
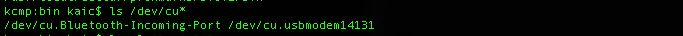
You should see a device named /dev/cu.usbmodemXXXXX where the XXXXX is a number. Use the CDC flasher to upgrade the bootrom:
Mine is “14131”
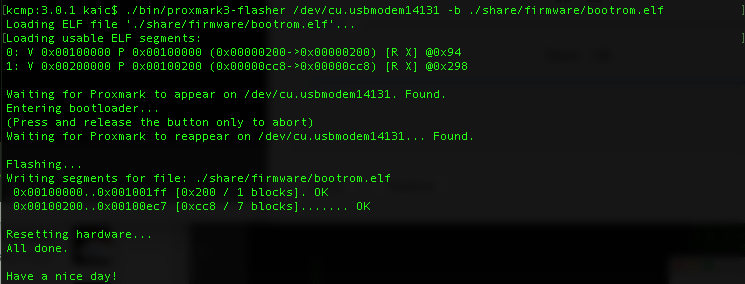
Flash the BootRom
./bin/proxmark3-flasher /dev/cu.usbmodem14XXX -b ./share/firmware/bootrom.elf
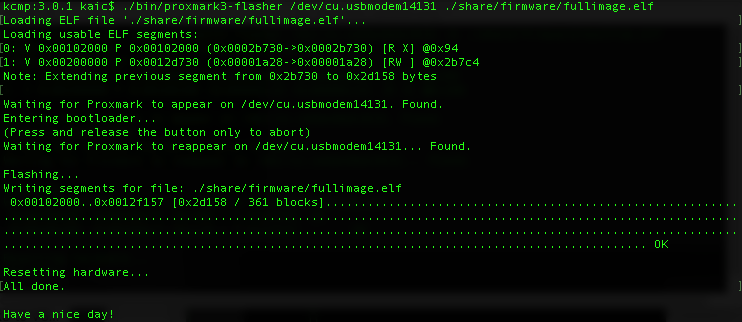
Update the FPGA and OS
./bin/proxmark3-flasher /dev/cu.usbmodem14XXX ./share/firmware/fullimage.elf
First use
So make sure that the Proxmark version number and usbmodem number are correct to yours.
/usr/local/Cellar/proxmark3/X.X.X/bin/proxmark3 /dev/cu.usbmodem14XXX
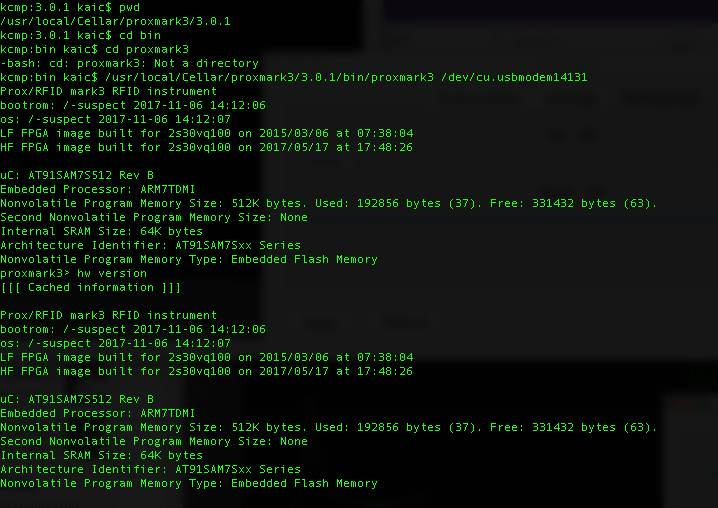
Can check the hardware version by running
hw version
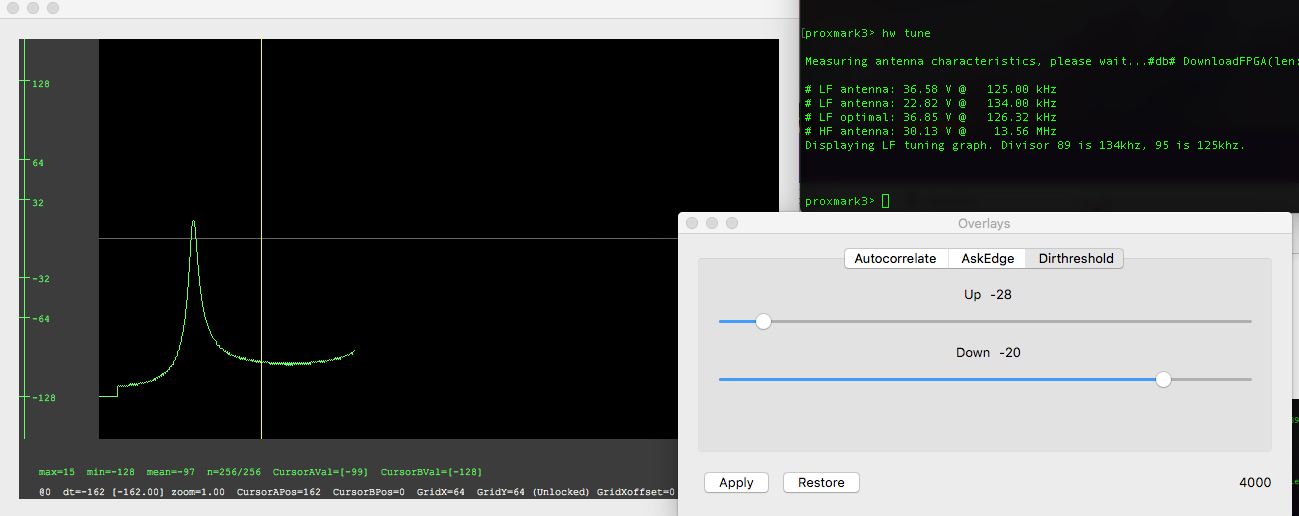
and run a simple hw tune to check it’s working.
hw tune
Recent Posts
Tags
Categories
Active directory Burpsuite Cheatsheet Crackmapexec Empire Events Exploit File transfer Iis Implants Kcsec Kerberos Kernelpop Ksec Ksec snapshot Lab Metasploit Metasploitable Msfvenom Netcat Nfc & rfid Nikto Nmap Pivoting Privilege escalation Proxmark Proxychains Redteam Responder Rubber ducky Shells Sqlmap Sshutle Thefatrat Toolkit Webapp Windows domain Xss



