Posts
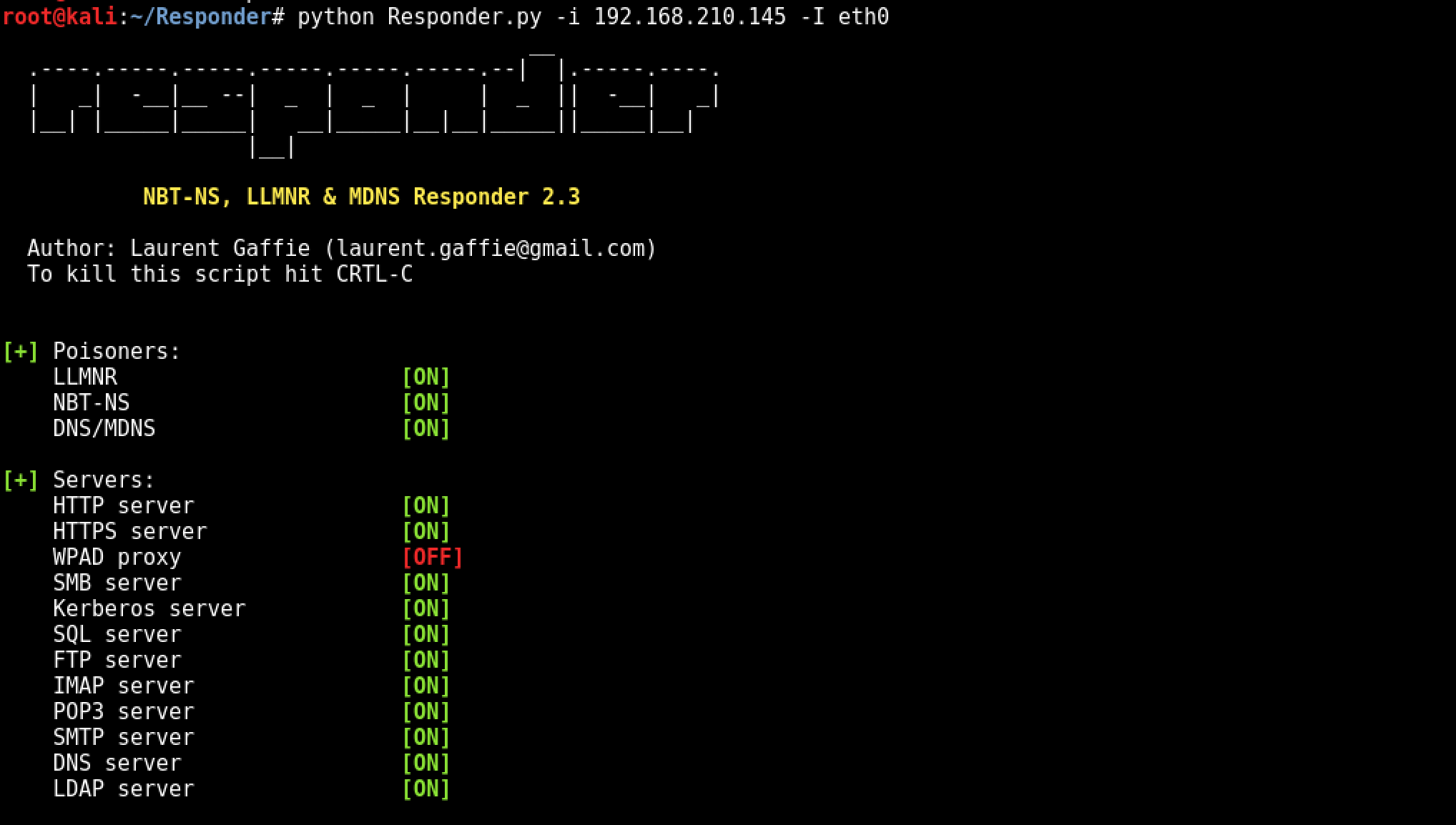
Notes Responder - Ultimate Guide Responder - Info Github Repo Orginal Blog post by Mucahit Karadag What is WPAD? Organisations all...

What is this site and who are we ? We are KSEC, Cyber Security is key to the world more than most know. That’s why we’...
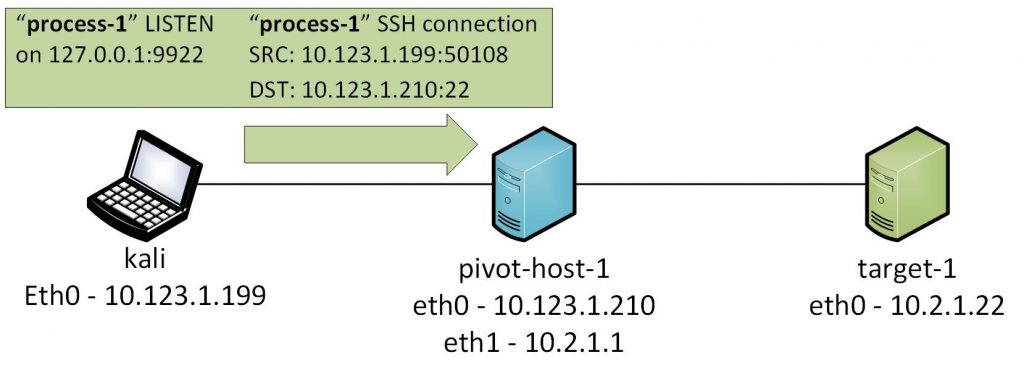
In part one of the SSH pivoting guide, I’ll provide a detailed (pedantic) guide of the easiest form of pivoting which is dep...

What is Pivoting ? Being able to access networks that we do not have access to by using a compromised server. You can there for ac...
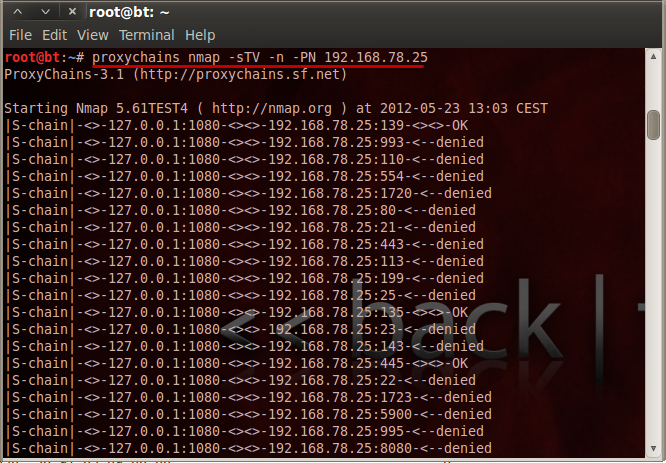
Transparent proxy server that works as a poor man’s VPN. Forwards over ssh. Doesn’t require admin. Works with Linux an...

Dynamic Port Forwarding is the third major method of port redirection with SSH. Where as previously both local and remote port for...

As seen in the above topology, the device that has two NICs has access to the both 192.168.1.0/24 and 192.168.10.0/24 networks. Un...
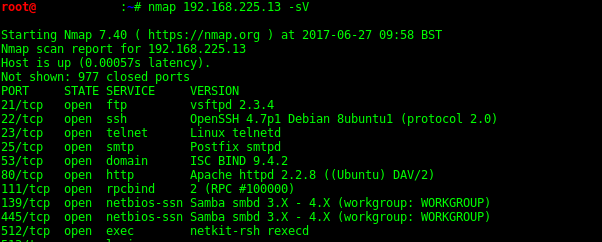
What is NMAP ? Nmap (Network Mapper), Is mother of all port scanners. Commonly used for network discovery and Service/Security enu...
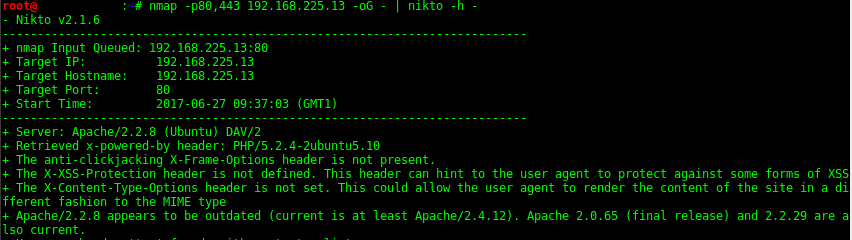
Nmap Nikto Scan Scans for http (Web) servers on port 80 and pipes into Nikto for scanning. nmap -p80 10.0.1.0/24 -oG - | nikto.pl ...
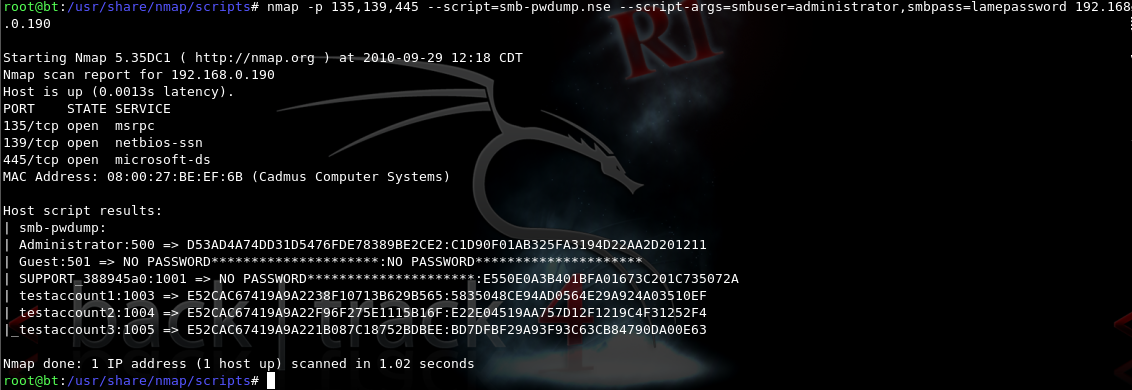
Scripts info Get help for a script nmap --script-help=ssl-heartbleed updating scripts nmap --script-updatedb Location and finding ...
Recent Posts
Tags
Categories
Active directory Burpsuite Cheatsheet Crackmapexec Empire Events Exploit File transfer Iis Implants Kcsec Kerberos Kernelpop Ksec Ksec snapshot Lab Metasploit Metasploitable Msfvenom Netcat Nfc & rfid Nikto Nmap Pivoting Privilege escalation Proxmark Proxychains Redteam Responder Rubber ducky Shells Sqlmap Sshutle Thefatrat Toolkit Webapp Windows domain Xss